Blast Radius: Why Agent Credentials Need Hard Walls
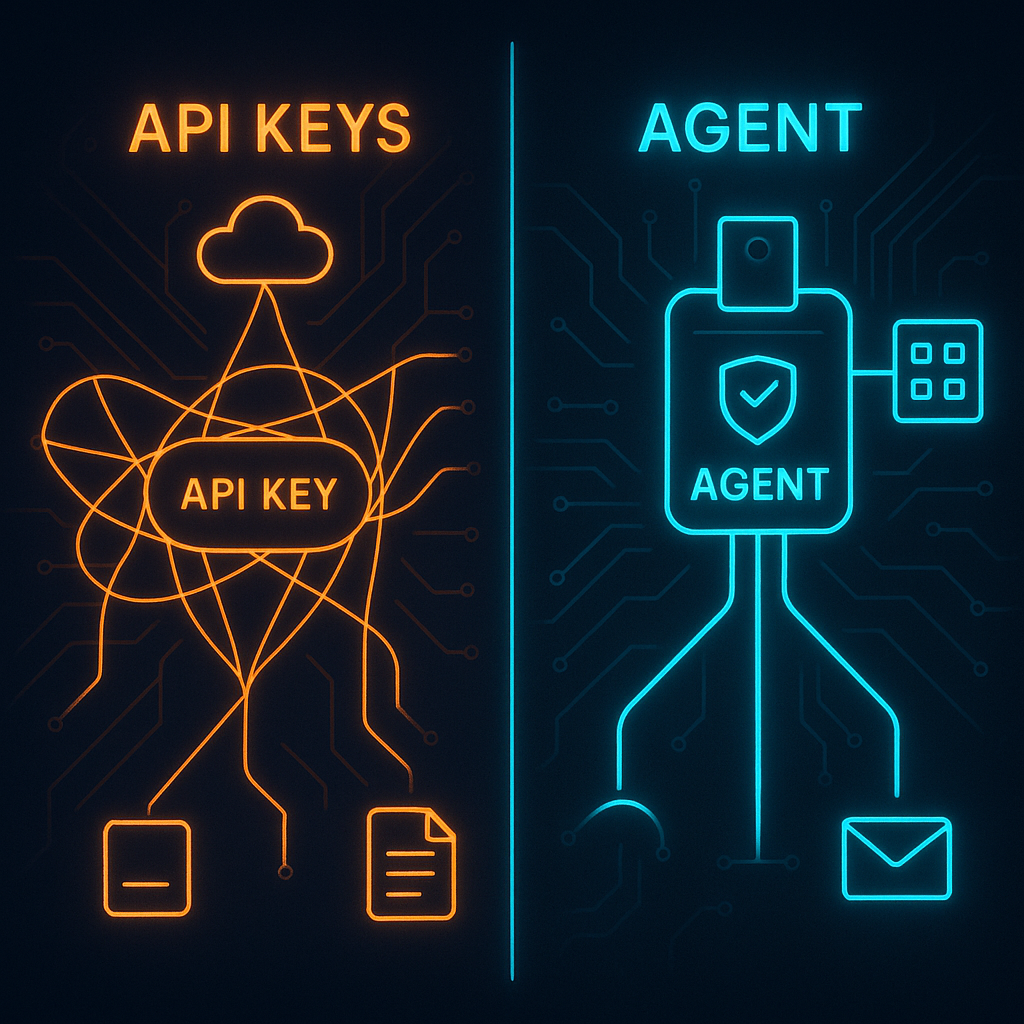
An agent that runs on your API keys is an agent with your blast radius. When something goes wrong — a bug, a misconfigured goal, a compromised prompt — it affects everything your credentials touch.
The fix is simple but often skipped: give agents their own credentials.
The short answer
Blast radius is the scope of potential damage when an agent malfunctions or is compromised. An agent using shared developer credentials has a blast radius equal to the full developer account. An agent with isolated, pre-funded credentials has a blast radius limited to what's been provisioned in its own account — making worst-case outcomes bounded and recoverable.
Blast radius is how much can go wrong when something does go wrong. An agent using your API keys or payment credentials has your full blast radius. An agent with its own isolated credentials has a blast radius limited to what’s been provisioned in its account. ATXP provisions per-agent accounts specifically for this isolation.
What blast radius actually means
Consider two scenarios:
Scenario A: Agent uses developer credentials
Your agent has access to your OpenAI API key, your Anthropic API key, your Stripe account, and your primary email. A loop bug causes it to make 10,000 API calls in 10 minutes instead of 10.
Result:
- OpenAI API bill: potentially hundreds of dollars in unexpected charges
- Anthropic API bill: same
- Your Stripe account: agent may have initiated transactions you didn’t authorize
- Your email: sent from your address, in your name
- Your API keys: may need rotation, breaking other systems that depend on them
Scenario B: Agent uses its own ATXP account
Same bug. Same 10,000 calls.
Result:
- ATXP IOU balance: depleted (agent stops when balance hits zero)
- Maximum financial impact: whatever was pre-funded in the agent’s balance
- Your credentials: untouched
- Recovery: fund the agent’s account again if the bug is fixed, or revoke and provision a new agent
The structural difference: in Scenario B, the ceiling is the agent’s balance. In Scenario A, the ceiling is your account limits — which may be much higher than you expected to spend.
The five blast radius risks with shared credentials
1. Spending runaway
Your API account has a limit that’s set for your use, not for an agent running in a loop. A bug that causes an agent to make 100x the expected calls will run up a real bill before any soft limit kicks in. With a pre-funded agent account, the ceiling is the balance — structurally, not as a soft limit.
2. Rate limit exhaustion
Some APIs have rate limits per key rather than per user. An agent hammering a rate-limited API at 10,000 requests per hour will exhaust your key’s rate limit — affecting every other service or process that depends on the same key.
3. No clean revocation
When an agent using your API key misbehaves, how do you stop it without affecting everything else? You rotate the key — which breaks every other system depending on it. With an isolated agent account, you revoke the agent account. Everything else keeps working.
4. Audit trail contamination
Your billing dashboard and API logs mix your activity with the agent’s. Understanding what the agent spent requires filtering your personal history. With isolated credentials, the agent’s activity is entirely in its own account — fully visible, fully separable.
5. Cross-agent contamination
If you’re running multiple agents on the same credentials, one agent’s misbehavior affects the others’ rate limits, billing, and access. Isolated credentials mean each agent’s behavior is contained to its own account.
How credential isolation works
Every ATXP agent account is isolated by design:
| Resource | Developer account | Agent account |
|---|---|---|
| Agent handle / identity | Developer’s identity | Agent’s own persistent handle |
| IOU payment balance | Developer’s payment | Agent’s pre-funded balance |
| Email address | Developer’s email | Agent’s own @atxp.email |
| API access | Developer’s keys | Agent’s access grants |
| Audit log | Developer’s full activity | Agent’s isolated transaction log |
| Revocation | Affects developer + all agents | Affects only this agent |
When you run npx atxp, the provisioned account is for the agent — not a proxy of yours. The handle is the agent’s. The balance is the agent’s. If something goes wrong, you revoke the agent account. Nothing else is affected.
Minimum viable isolation checklist
Even if you’re not using ATXP, these practices reduce blast radius for any agent setup:
- Never use your primary API keys for agents — create sub-keys or scoped keys where your provider supports it
- Set API-level spend limits where available (OpenAI supports hard usage caps per API key)
- Use a separate payment instrument for agent spending — a virtual card with a low limit, or a pre-funded account
- Scope API access — give the agent the minimum permissions it needs, not admin access
- Maintain separate audit logs — if logs mix, filter by IP or agent identifier to separate activity
- Document the revocation path before you need it — what do you do when this agent needs to be stopped immediately?
The last one matters more than it seems. In an incident, you want to know the revocation path before you’re in it.
The revocation playbook
When an agent needs to be stopped immediately:
With ATXP:
npx atxp revoke --agent "agent-name"The agent account is deactivated. Its balance is frozen. Tool calls from the agent stop returning successful responses. Your account is untouched.
Without isolated credentials:
- Identify which key the agent was using
- Rotate the key
- Update every other system using that key
- Audit the billing history for the compromised period
- Dispute any unauthorized charges
The ATXP path is one command. The non-isolated path is an incident response process.
# Provision an isolated agent account
npx atxp
# Check what the agent has access to
npx atxp status
# Revoke if needed
npx atxp revoke --agent "agent-name"10 free IOU tokens on registration. Per-agent isolation by default. Docs →
Frequently asked questions
What is blast radius for AI agents?
How much damage can occur when something goes wrong. Shared credentials = your full blast radius. Isolated agent credentials = limited to the agent’s provisioned resources.
Why shouldn’t my agent use my API keys?
No structural spending ceiling, no clean revocation path, no accountability separation, rate limit exhaustion risk affecting your whole account.
How do I limit blast radius?
Give the agent its own ATXP account with an isolated IOU balance and agent handle. Blast radius is then limited to the agent’s pre-funded amount.
What is credential isolation?
Each agent has its own credentials separate from the developer’s and from other agents — own handle, own balance, own access grants, own audit log.
What if an agent’s credentials are compromised?
With ATXP isolation: npx atxp revoke --agent. One command. Your account untouched. Without isolation: rotate your main key, audit everything, update all dependent systems.
Does ATXP provide isolation?
Yes. Every ATXP agent account is isolated by default — own handle, own balance, own log. Are AI agents safe? →